Alert fatigue is a far too common problem that spans a multitude of industries. Cybersecurity, home security, aviation, and even healthcare are all impacted by alert fatigue. And that’s just to name a few.
When alert fatigue sets in, and we become desensitized to alerts, the results can be catastrophic: our safety may be at risk. In healthcare alert fatigue can lead to medical errors that put patient health at risk. In cybersecurity, siem alert oversight can take down the critical infrastructure that we depend on to keep our society safe. Alert fatigue is an urgent problem that jeopardizes security.
So what can we do?
Alert fatigue is a serious problem in cybersecurity, but there are solutions to help. One of the most effective solutions that we’ve found is to increase the quality of alerts that you receive from your siem. What we mean by this is the need to better the process of siem alert validation to validate the threatening alerts from those that are false positives and benign. We can then be sure that the alerts we receive actually present a threat. In doing so, we lessen the number of alerts received and reduce alert fatigue. We can then focus on the quality alerts – the ones that need our attention.
3 tactics to validate siem alerts
Below we present 3 steps to validate the true siem alerts and filter out false positives. Improved alert quality means that we can be lazer-focused on the most threatening alerts.
1. Ditch the manual tasks and adopt automation
On any given day cyber analysts receive an unmanageable amount of threat data. The excessive threat data clouds alert insight. It becomes exceedingly difficult to know which alerts are false positives. The lack of visibility increases the risk of overlooking threats and leads to errors in decision-making.
Analysts should utilize automation to analyze threat data. Automation takes care of the tedious tasks of data analysis, minimizing the amount of data analysts have to deal with. Automation greatly lessens the workload. Analysts gain the time needed to manage complex breaches rather than focus on the mundane tasks of identifying potential threats. Automation can also be used to automatically delete malicious activity, reducing human error that may fail to notice the threat.

2. Understand your unique threat environment
Just as important as automation is the need to know the threat environment well; every organization has a unique threat environment. Knowledge of the threat environment is necessary to know which log sources to attach to your siem alerts. With the right log sources attached, we can validate that the alert is an actual threat and not a false positive.
Logs add data context to alerts. We get a better understanding of where the alerts are coming from, the actors behind them, and how threatening they are. The right data context helps us get actionable insights on our alerts. We can then execute the right response.
Besides log sources, we can improve siem alert validation with technology that leverages AI/ML personalized to the unique threat environment. Personalized AI/ML surveys the threat landscape for similarities between alerts. The machine learning algorithm then recommends new tuning rules based on the similarities. We can then remove the alerts that match in similarity to clear out noise and false positive alerts.
3. Look to ML models that incorporate analyst feedback
To get the most from AI/ML tuning, we should utilize ML models built with analyst feedback. ML models that use analyst feedback are more reliable and adaptable to varying threat landscapes. As the front-line defenders, analysts have a thorough understanding of the threat landscape and the types of alerts they receive. By incorporating their unique knowledge into ML models, we can reliably validate alerts and then predict and prioritize our alerts.
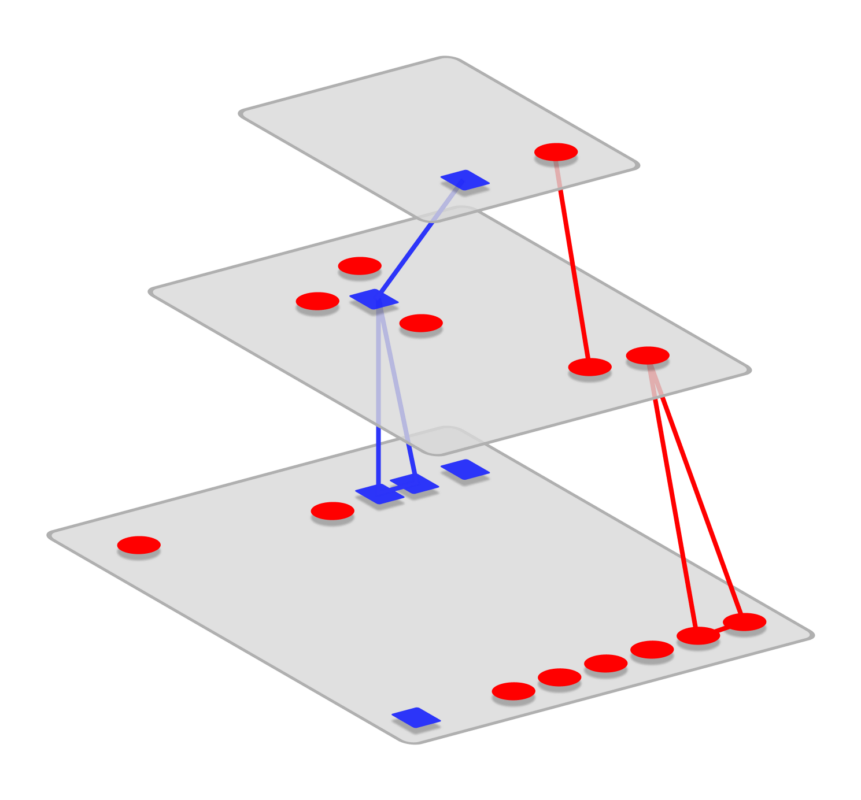
4. Leverage graphs to minimize unnecessary data and strengthen the analysis process
Minimizing unnecessary threat data makes the alert validation process faster and more productive. A great way to minimize threat data is through the use of accessible, multidimensional graphs. User-friendly graphs that present the exact data users need, when they need it – and nothing more – lessen cognitive strain and alert fatigue. Graphs spotlight the data that is needed in a given analysis scenario. Graphs make data accessible and accelerate the analysis process. You can trust that all incidents are identified and stopped.
Siem alert validation final thoughts
Proper alert validation is crucial to defend against advanced cyber attacks; it’s imperative to separate false positive alerts from significant alerts. Otherwise analysts risk alert fatigue.
Thankfully, there are solutions to automate and streamline the alert validation process. To improve alert validation and reduce alert fatigue, adopt SaaS add-ons that integrate into existing siems, such as Microsoft Sentinel. With greater context and faster alert tuning, integrated siem add-ons make it easy to filter out false positives and implement safer cybersecurity responses. Check out Seculyze to learn how Microsoft Sentinel add-ons automatically validate alerts.







