Key consideration
Does your security architecture match your risk appetite?
About Security Architecture: Purpose
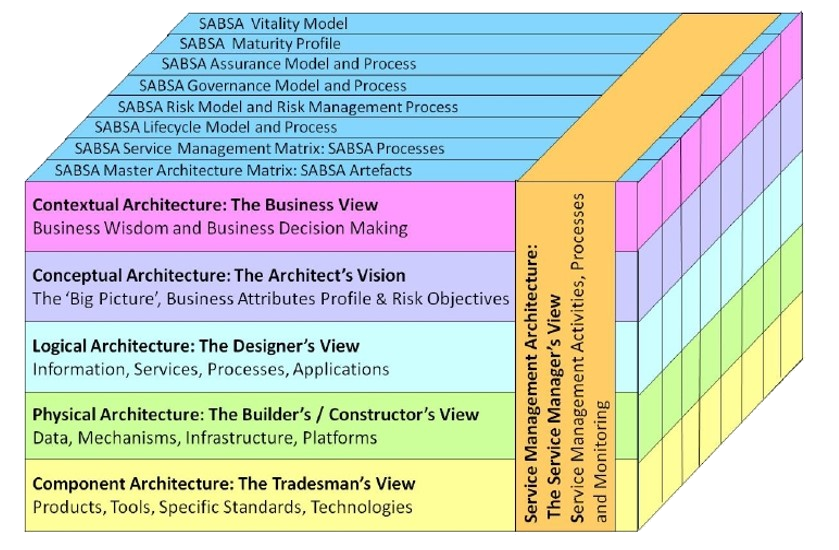
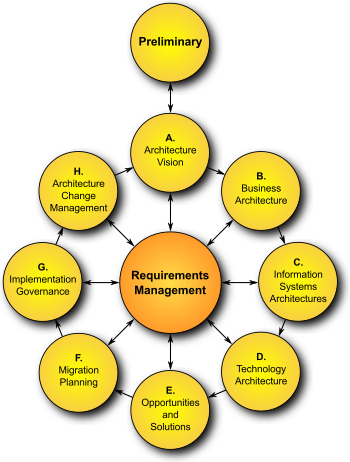
The purpose of security architecture is to ensure alignment of business strategy and IT security. It should ultimately allow for traceability from the business strategy to the underlying technology.
The important end-product is to help departments understand the business model, articulate business risks and build an IT setup that supports Security architecture. It can be viewed as a subset to the enterprise architecture, but also as an individual discipline. In Seculyze, we have worked with both.
Top 5 Benefits of Security Architecture
While security architecture consists of resources and components of a security system, it sets the direction for the security design which includes techniques and methods. This ultimately facilitates security in hardware and software.
Security architecture ensures alignment of the business strategy and IT security – and hence builds the bridge between business, IT, and security. As a side effect, projects and features can be rolled out more quickly.
An architecture and plan provide the basis for informing internal and external stakeholders of the current and future situation in a prompt manner. It gives the opportunity to effectively collaborate and work toward accomplishing shared goal.
Artifacts can serve as proof e.g., when a company needs to obtain certifications. It is therefore easier during the initial certification or re-certification that the processes are “lived”. Reuse reduces the time and effort required for testing and facilitates the use of existing interfaces.
It is possible to develop modular, secure IT with standardized components that have built in security and already tested. This ensures that IT is used in a consistent manner and promotes clear responsibilities. Furthermore, it reduces costs with fewer components used by numerous apps.
Want to know more about Security Architecture?