Microsoft Sentinel is an important tool to combat cyberattacks. But as organizations receive a growing number of alerts, coupled with a shortage of staff and resources to manage those alerts, analysts are finding themselves overwhelmed. Many of the alerts they receive are false positives, leading to wasted time and effort – and the risk of alert fatigue. So, let’s cut to the chase: Microsoft Sentinel is falling short, and its capabilities need to be greatly improved. Our Microsoft Sentinel tips will help you get more from Microsoft Sentinel and improve its capabilities.
Analysts need more from Microsoft Sentinel to react faster and better against high-risk threats. For analysts to increase their ability to fight advanced threats they need to quickly pinpoint which threats to prioritize. Doing so requires distinguishing mere suspicious activity from real, malicious events. Tuning alert thresholds is the most straightforward solution to prioritize threats. But regularly tuning and reconfiguring Microsoft Sentinel can be resource and time intensive. Not to mention that storing and integrating log sources needed to understand cyber threats is an expensive endeavor. Thankfully, there are ways to improve the performance of Microsoft Sentinel to generate a faster and better threat response, all the while reducing the overall costs.
In this blog post, we share 5 Microsoft Sentinel tips to unlock Microsoft Sentinel’s full power. Follow these 5 Microsoft Sentinel tips to reduce alert fatigue, gain improved threat detection and response, and decrease the risk of cyberattacks.
Review and test alert rules to keep them up to date
The threat landscape is constantly changing. So is cybersecurity technology and IT infrastructure. Microsoft Sentinel alert rules need constant up-keep and reconfiguration to function properly. Alert rules should be kept up to date so that they are guaranteed to trigger when encountering a real threat but are not so sensitive to trigger false positives. If alert rules are not regularly kept up to date, you run the risk of triggering too many false positives, rendering the alert rules ineffective. Analysts risk entering states of alert fatigue and missing incidents. Microsoft Sentinel still generates too many false positives, contributing to the problem of alert fatigue.
That said, we believe that Microsoft Sentinel is the best solution on the market, but it can be greatly improved with the ability to automatically review and test alert rules to match the fast-changing threat landscape and decrease false positives. Look to technology add-ons to get more from Microsoft Sentinel and improve your ability to regularly review and test alert rules – a necessity for reducing alert fatigue.
Focus on reducing the number of alerts you receive
Time for the second tip of our Microsoft Sentinel tips. Many security analysts experience that Microsoft Sentinel generates too many alerts. As mentioned, a large portion of these alerts are false positives. If you can eliminate the alerts that pose little to no threat, then you gain the breathing space to only focus on the high-level threats, improving threat detection and response.
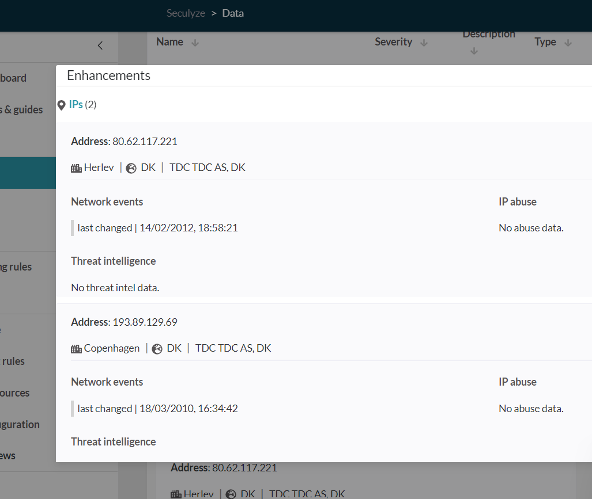
Keeping your alert rules up to date is a necessary step to weed out irrelevant alerts. Additionally, your alert rules should be enriched with threat data to add more context and gain a clearer overview of the threats. The screenshot below is an example of Microsoft Sentinel-integrated software that automatically adds threat context to alerts to quickly pinpoint which alerts are worth focusing on and which can be discarded.
Integrating the right log sources into Microsoft Sentinel is one way to gain the added threat context. This brings us to the next tip of our Microsoft Sentinel tips.
Assess your log sources to prioritize the logs that best fit your needs
To execute an effective threat detection and response you want to make sure that you have the context needed to understand your threats. Data context is a must to get actionable insights on your threats. To get the right data, make sure that you are integrating the right log sources into Microsoft Sentinel. Log sources help you understand your threats – who is attacking and how the attack is being implemented. You can then quickly decide on the best response.
Unfortunately, Microsoft Sentinel provides no straightforward solution to know which log sources to prioritize. But by utilizing additional software that integrates into Microsoft Sentinel, you gain best practice recommendations on which log sources to prioritize. The recommendations are based on an assessment of the needs of your organization – where your biggest vulnerabilities are located and what infrastructure is most critical to protect. The software also assesses the alerts you receive, determining which alerts need greater context, and which log sources are necessary to get that context. Prioritize the right log sources to cover any blind spots and vulnerabilities. Time for tip four of Microsoft Sentinel tips.
Prioritize high-value log sources to keep costs low
The cost of deploying Microsoft Sentinel skyrockets when you factor in log sources and storage. To keep costs low, limit the amount of data you ingest. Doing so means that you can reduce noise and stay focused on the data that is necessary for your needs and provides value for your goals and use cases.
At the same time, you want to pinpoint high-value logs. High-value logs are those that have the lowest integration cost but provide high gains.
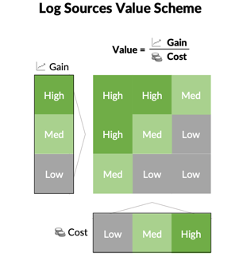
Look for additional tools that automatically provide an overview of the costs of enabling or disabling log sources, including an estimated cost per log source. Software that functions as an add-on to Microsoft Sentinel makes for a seamless process. Now to Microsoft Sentinel tips 5.
Leverage the benefits of threat intelligence such as OSINT, to stay in tune with the changing threat landscape
Alongside log sources, threat intelligence such as OSINT (Open-Source Intelligence) provides added context to your alerts. By enriching your alerts with threat intelligence, you can better understand where your threats are coming from, their target, and who the actors are. Clear insight results in a better and faster threat response. Enriched alerts vastly improve the capabilities of Microsoft Sentinel.
OSINT is data gathered from public sources and may include social media data, news data, survey data, location data and much more. But for OSINT to be an effective resource, it first needs to be normalized and converted into actionable threat intelligence. Additional software that integrates into Microsoft Sentinel can automate this step.
Once the data is normalized, the new threat intelligence allows for easy recognition of patterns and the correlation of events. With the benefits of clearly understanding your threats, threat intelligence is truly a vital weapon in the fight against cyberattacks.
That just about wraps it up. Last but not least: the conclusion to our Microsoft Sentinel tips.
Conclusion to Microsoft Sentinel Tips
To meet the fast changes in the threat landscape and the increasingly advanced methods of cyberattacks, security analysts need more power from Microsoft Sentinel. This includes resources to accurately pinpoint high-risk threats, remove false positive alerts, and reduce alert fatigue. Seculyze is SaaS that integrates into Microsoft Sentinel to simplify the security process.
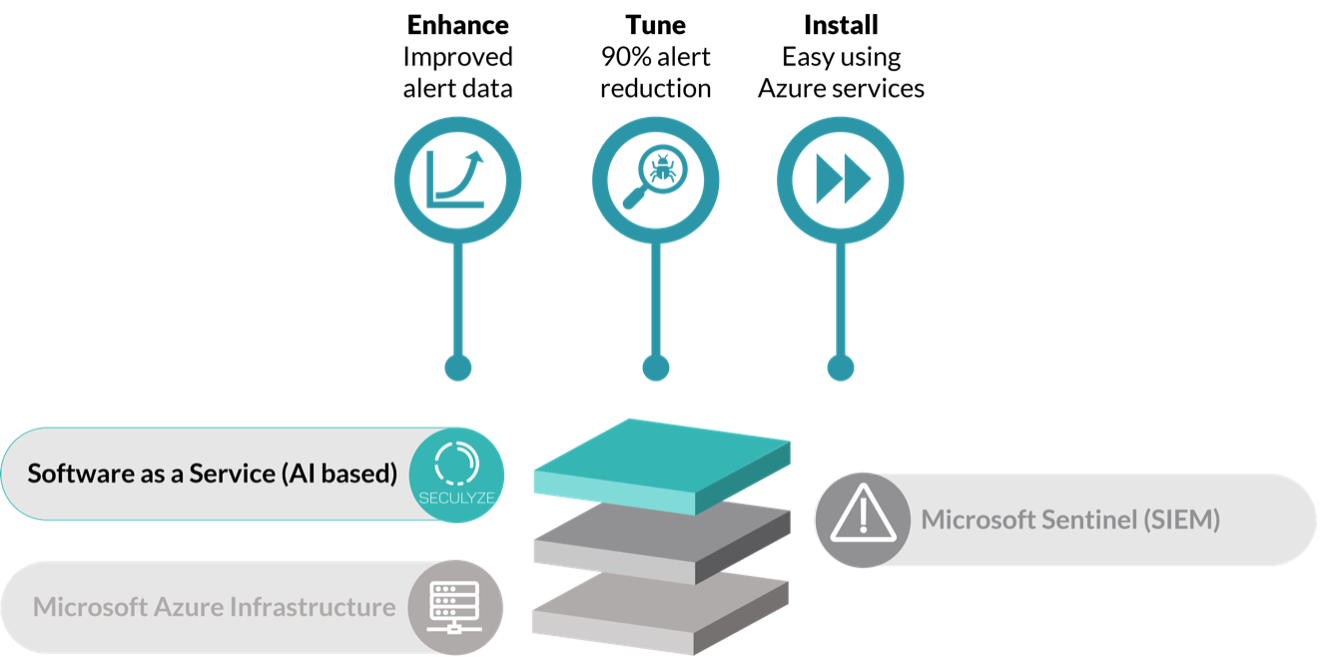
With automated alert Enrichment, Tuning, and Health Check, the software enhances the capabilities of Microsoft Sentinel. Analysts can now enact a better, simplified, threat detection and response. Reduce alert fatigue and greatly decrease the risk of cyberattacks.
If you found our Microsoft Sentinel tips useful, you can learn more on our website: https://seculyze.com/.
Follow us on LinkedIn and Twitter for more insights on how to decrease the risk of cyberattacks.







